Blog by Kem Gay, Sr. Intelligence Analyst, Constella Intelligence
Trained to Question and Doubt Everything
As an intelligence analyst, I was properly trained for this environment. I’m quite familiar with various cyber threats targeting industries, employees, and everyday citizens. These types of acts are perpetrated by nefarious actors attempting to steal personally identifiable information (PII) and trade secrets, ultimately leading to collateral damage.
Therefore, good cyber hygiene is part of my everyday routine — — avoiding suspicious emails, using strong unique passwords, keeping my software updated, protecting my devices with antivirus and malware tools, etc. However, in the past four months, I have been surprised at the sophistication and creativity of recent phone scams directed my way.
Phone Scam Trends
Many people consider phone scams as a dated deception technique compared to the virtual world with which we interact on a daily basis. Phone scams usually involve robocalls, the promise of free trips and investment schemes. These scams were once easily identified since most would come from out-of-state numbers.
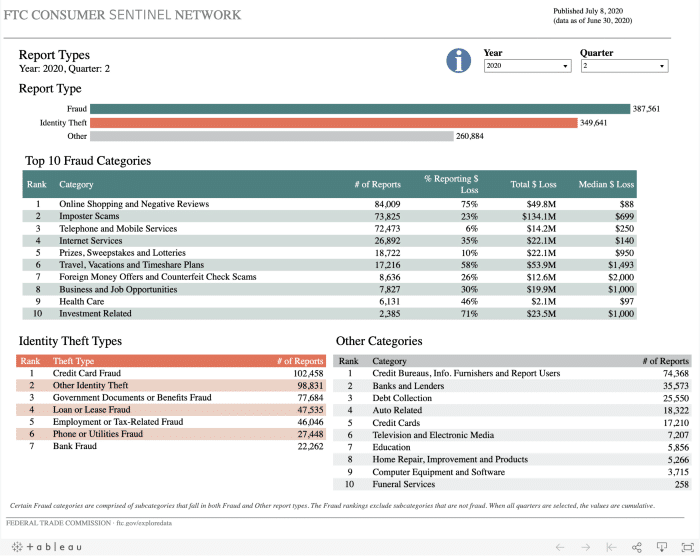
However, with spoofing technology, fraudsters can easily change the incoming number seen on caller IDs making it more difficult to detect. According to the Federal Trade Commission’s Consumer Sentinel Network, as of June 30, 2020, Imposter Scams were ranked 2nd in all reported cases of fraud.
Apple Support Phone Scams
I recently received several consecutive phone calls from an unknown number on a Friday evening. I have a habit of not answering such calls, as they are usually spam. I was finishing up work and looking forward to finally spending some social distancing time with my girlfriends. I was surprised when a voicemail was left and even more shocked when the caller stated he was a technician from Apple Support and was reaching out because there was suspicious activity from my iCloud account. I was preparing to return the call when my phone rang again. The technician appeared to be calling from a call center environment, as I could hear the voices of other technicians asking routine questions to unsuspecting victims.
For anyone familiar with this type of fraud, the fraudster has two objectives. First, get the victim to share a computer screen with him/her to likely install malware to steal PII and other financial information. Second, lure the victim away from the computer for additional probing by instructing them to go purchase a gift card. Luckily, I didn’t fall victim to this scenario, but I was impressed with the scale and sophistication of this scheme. At one point when I pressed the fraudster to provide me with information to confirm my account, he transferred me to a manager. When I hung up on the caller, he subsequently called me eight times and even sent a text message asking “if everything was alright.”
Fraudsters attempt to exploit the fact that people want reputable businesses, especially a company like Apple, to have their best interest in mind and notify them if there are any technical discrepancies. Apple doesn’t call consumers and advises users who receive unsolicited or suspicious phone calls from someone claiming to be from Apple to hang up the phone.
Court Case Phone Scam: with a Psychological Twist
In another sophisticated scam, I received a voice message from someone claiming to be an investigator from county court services looking for a relative residing in another state.
The caller stated that my number was provided as a possible location of the relative and they needed to call to prevent a court case from proceeding. I immediately reached out to the relative in question, who stated he had received a call from a friend who said the exact same thing.
Over the course of four hours, six other family members were contacted. No one knew who this “investigator” was and the relative did not have any pending legal issues. Interestingly, the only demand of the caller was to relay the message — a tactic that seems counterintuitive for a suspected fraudster.
Eventually, the relative in question called the “investigator” who in turn asked for his Social Security Number (SSN) and date of birth (DOB) to verify his alleged court case, most likely a ploy to steal his PII. When this information wasn’t provided, the “investigator” threatened the relative with jail time. A quick internet search revealed this type of call was a prevalent scam in the area where my relative lives.
This phone scam was unique because it questioned one’s reputation. At a psychological level, most people care about what others think of them and the fear of social censure from peers can be demoralizing. This fraud is most likely used to unsettle victims, leading them to call back the “investigator” and disclose any information asked of them.
Service Industry Related Phone Scams
Just last week, fraudsters using telephone spoofing technology posed as staff at The Ritz London hotel to steal credit card data from customers staying at the hotel. It’s clear these scams aren’t going away anytime soon. As we interact in the virtual world, we must keep our guard against the deception of fraudsters who are using new techniques for the same ol’ phone scams.
Take Action: Report. Phone Scams to the FCC
Although the Federal Communications Commission (FCC) has made combatting unlawful robocalls and malicious caller ID spoofing a top consumer protection priority, fraudsters continue to evade and find creative ways to lure victims through their mobile phones. This COVID-19 crisis has created a perfect environment for phone scams as more people are home and connected to their phones. In the past seven months, the FCC has received approximately 35K complaints. Be sure to file yours and help combat malicious scammers.
For additional information on avoiding spoofing scams, see the FCC Tip Card.
Interested in our work? Please contact us at info@constellaintelligence.com. To learn more about Constella, subscribe to our newsletter below.