Investigate anonymous threat actors by identifying and attributing anonymous risks targeting your organization with Hunter OSINT Investigations.
Read how leading cyber investigative journalist Brian Krebs used Constella Hunter to fight against cybercrime:
Constella’s Role in Fighting Cybercrime: Supporting Investigative Journalism and Law Enforcement
Today’s cybercriminals are more advanced and better funded than ever before. They operate with a high level of anonymity, using underground forums, aliases, and cryptocurrency to obfuscate their activities and hide their identities.
This makes your job of disrupting these adversaries increasingly difficult, requiring innovative data scouring and collection methods to uncover critical intelligence that will move an investigation forward.
Constella Hunter is an intuitive cyber investigation tool that enables you to rapidly attribute malicious activity, fraud, and potential insider threats. With Hunter, you can analyze data from thousands of sources, collate and compare it across sources, and identify unknown connections and networks of activity.
Hunter delivers real-time and historical identity intelligence that helps you solve cases 5X faster. Hunter discovers the hidden connections that other tools and teams miss with its unique analytics engine and massive scalability. Hunter is designed to accelerate and simplify investigations and threat analysis by:
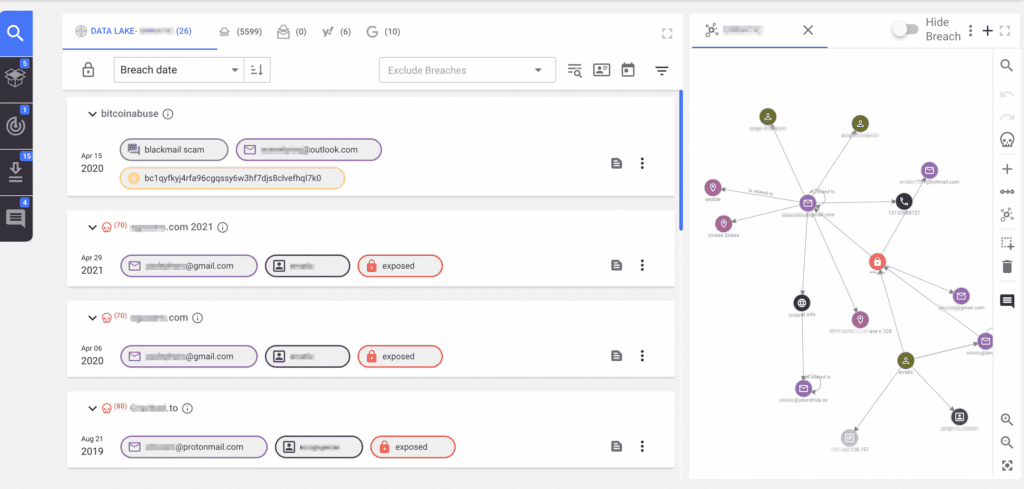
Hunter collects data from across the Surface, Deep, and Dark Web, and social media. It combines data from these thousands of sources with the Constella Data Lake™, containing over 124 billion compromised identity records, delivering unmatched visibility of threat actor activity.
Start with a single indicator and enrich information from other sources and begin making connections, in real-time.
Correlate activity across data sources to identify new accounts and data associated with your target.
Build data visualizations in a graphical format that enables you to understand links and conduct advanced analysis.
Create profiles automatically based on commonalities of results using the AI-based classifier.
Focus your search using a simple and intuitive search bar. You can search for over 30 different attributes and keywords across multiple sources (either individually or one at a time).
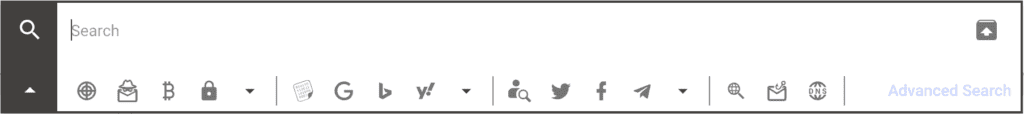
Link data from Surface, Deep, and Dark Web and Social Media sources and easily move between them.
Search the Constella Data Lake™ to access 124+ billion compromised identity records.
Conduct a bulk search, identify related searches, view your search history and investigate domain exposure.
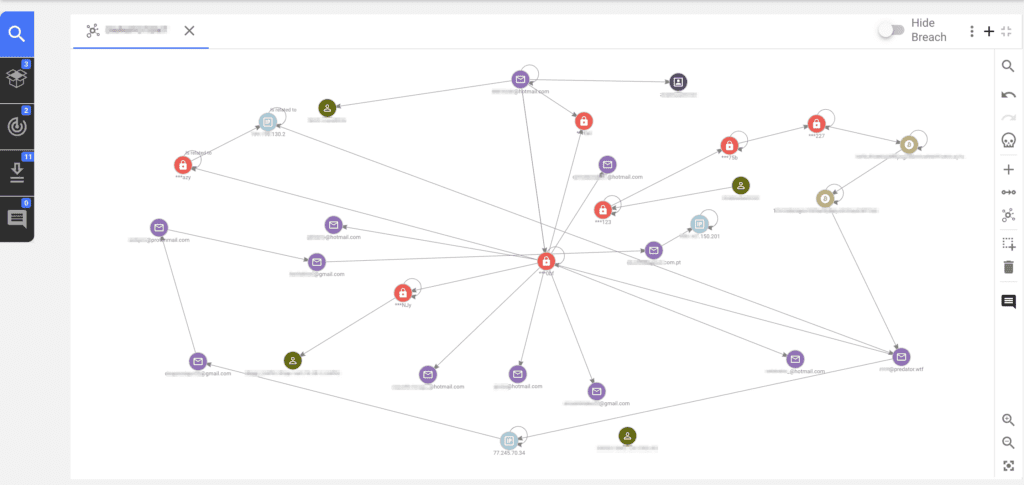
Discover hidden connections and tools that fuel criminal activity.
Break down traditional barriers across data silos; Link real identity information to obfuscated identities & malicious activity: solve investigations 5x faster.
Build and collect evidence and submit to LEA / Dept of Treasury; decrease losses and reduce risk of future attacks.
The Constella team consists of intelligence community analysts, infosec pioneers, military veterans and tech entrepreneurs with a single mission: Empower organizations to know their adversary and disrupt malicious activity.
Many of the largest and most successful security and services providers rely on Constella Intelligence to create new revenue streams and improve customer retention. As our partner, you receive comprehensive visibility into your customers’ external digital footprints, enabling you to deliver significant value to your customers.
MORE INFORMATION
Subscribe To The Constella Newsletter
© 2024 Constella Intelligence. All rights reserved. Website Privacy Policy. Terms of Use. Datalake Privacy Notice. Acceptable Use Policy.